Counter Surveillance
Stop listening devices and audio bugs by creating a perimeter of white noise that disables the audibility of anything recorded. All conversations, no matter how loud, will sound like static when the audio is played back.
White Noise Generator
Protection from eavesdropping meets the blended performance of this handheld, battery operate White Noise Generator. The J1000 creates an additional barrier of noise interference, reaching out farther than other models, making it possible to mask your conversation when confidentiality is necessary.
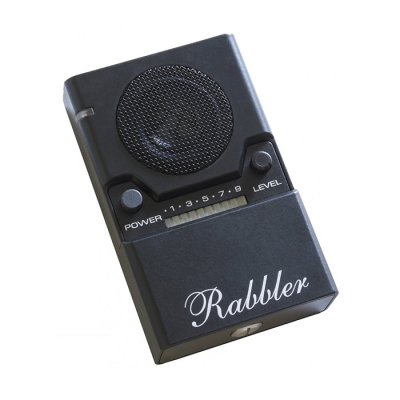
Rabbler Noise Generator
Protect from eavesdropping using the NG3000. The Rabbler creates an additional barrier of noise interference making it possible to mask your conversation when confidentiality is necessary.
Druid Noise Generator
Conceptually unique, the Druid succeeds where complicated eavesdrop countering devices fail. The NG5000 eliminates the expensive bug sweeping services; it eliminates complicated installation of sound masking systems, and provides the sanctity needed for your most confidential boardroom conversations.
Transducer for White Noise Generator
The TD2300 vibroacoustic transducer is part of a complete counter surveillance protection system. It inducts noise into walls, floors, ceilings, windows and other surfaces of the building,preventing leakage of sound signals. To provide a sufficient level of protection the system consists of a number of transducers installed on different structures in the room and is connected to the DNG-2300 generator.
Omnidirectional Speaker for White Noise Generator
White noise generators are widely used for protecting premises against acoustic leakage eavesdropping. The SP2300 omnidirectional speaker is an important component for such system. While the transducers inject the generated noise into the surfaces and structures stopping distributing of sound through them, the role of the speaker is to fill voids, cavities and ventilation shafts with the audio interference to prevent leakage of sound through the air.
Phone Safe Ultra - NG4100
Stop accidental info leakage in conference rooms or group meetings with the PHONE SAFE ULTRA. Mobile phones have an infinite number of benefits for communication and business; however, they also create certain threats of information leakage. One of the potential leakage channels is the phone's microphone picking up surrounding acoustics with a high sensitivity. The PHONE SAFE ULTRA has been developed by information security professionals to protect against this exact type of threat.